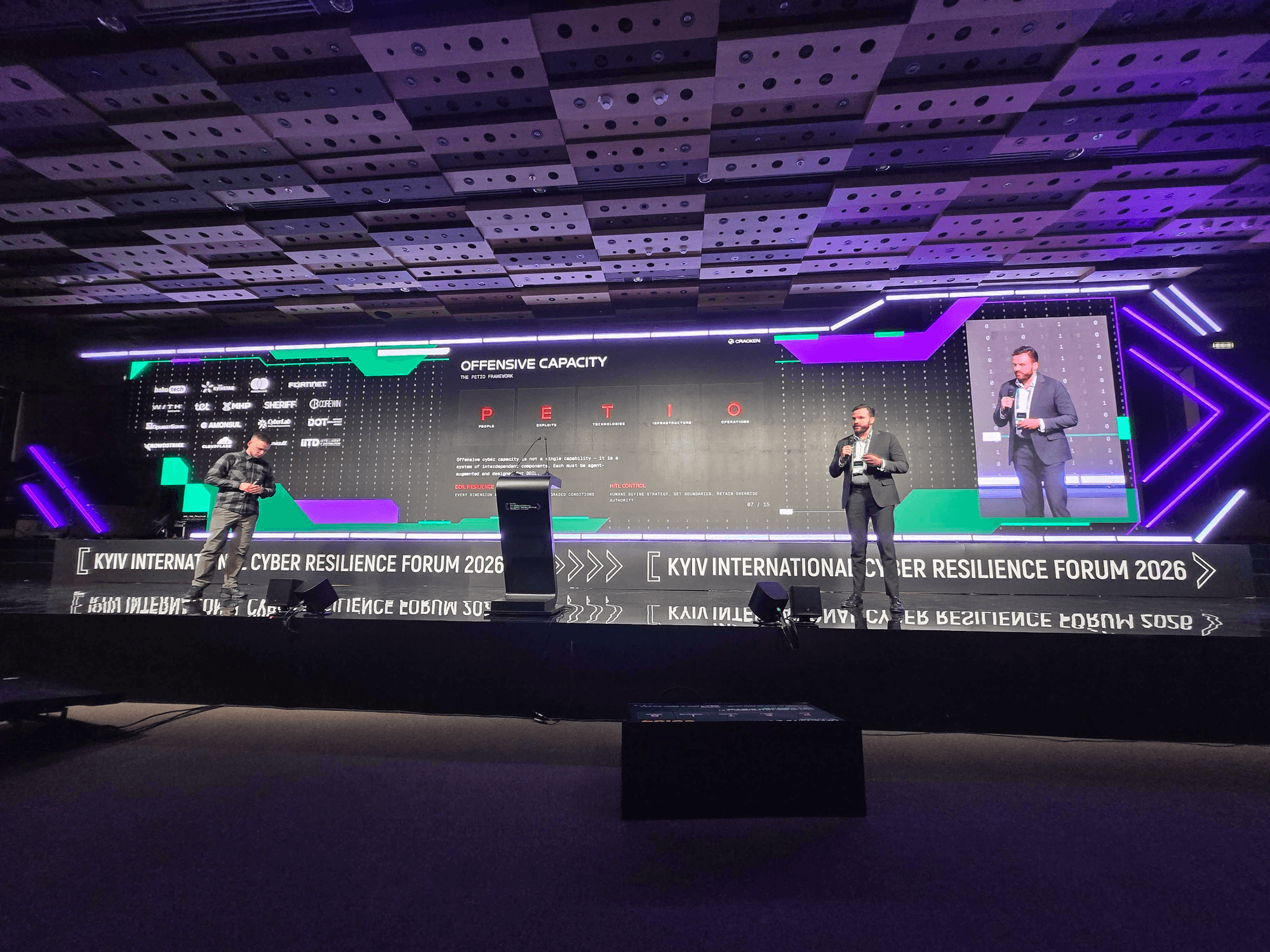
Cyber Capacity as a Systemic Model: Agent-Augmented Defense and Offense in DDIL Environments
Presented at the Kyiv International Cyber Resilience Forum 2026 by Jesse Nuese, Vlad Tereshyn, and Dr. Oleksii Baranovyski
What does a military staff officer actually do?
They don't make strategic decisions — that's the commander's job. They take high-level intent and translate it into concrete operational steps across complex, messy, real-world conditions. They coordinate between units that don't share systems. They maintain situational awareness when information is incomplete. They keep the operation moving when the plan breaks on contact with reality.
Now imagine that function — not the decision authority, but the translation and coordination layer — embedded in cyber operations. That's the central idea we presented at the Kyiv International Cyber Resilience Forum: AI agents as digital staff officers for national cyber capacity.
Not chatbots bolted onto dashboards. Not LLMs scanning log files. Staff officers — taking human strategic intent and translating it into technical execution across heterogeneous infrastructure, under conditions where connectivity, power, and personnel can disappear at any moment.
The problem with how the industry uses AI
Most cybersecurity vendors are plugging large language models directly into detection pipelines. Every alert, every log line, every network anomaly gets routed through expensive inference. The economics are upside down: defenders are burning their most expensive cognitive tool to process the adversary's cheapest output. Attackers generate massive event volumes with cheap scripts. Defenders pay per token to analyze each one.
In a well-connected enterprise environment, this model is merely wasteful. In DDIL — Denied, Degraded, Intermittent, Limited — it collapses. When a kinetic strike takes out your connectivity, your LLM-based detection goes dark. You're blind at exactly the wrong moment.
Ukraine's cyber operators don't have the luxury of assuming stable infrastructure. DDIL isn't an edge case for them — it's Tuesday. Rolling blackouts create unpredictable availability windows. Personnel exhaustion and equipment loss compound the problem. Any architecture that depends on persistent cloud connectivity is an architecture that fails under fire.
Cyber capacity is a system
We frame national cyber power as two interdependent capacities — defensive and offensive — that form a single system. Weaken one and you directly degrade the other. Both are under simultaneous kinetic and cyber attack in Ukraine, which means any framework that treats them as separate workstreams is already wrong.
The digital staff officer concept applies across both. On the defensive side, agents orchestrate detection, correlate across data sources, and implement policy decisions — while deterministic systems handle the raw volume of event processing. On the offensive side, agents decompose complex operations into executable steps, coordinate tool usage across teams, and maintain operational memory that persists across sessions. In both cases, humans set direction and agents handle the translation into action.
Three layers, always: human intent at the top, agent orchestration in the middle, deterministic execution at the bottom. Detection must be deterministic. Agents orchestrate. Humans command.
Why this architecture survives DDIL
The staff officer model holds up under degraded conditions because it's designed around two constraints that most AI architectures ignore.
First, autonomous continuity. When connectivity drops, the digital staff officer keeps working within pre-authorized parameters, logging everything for later review. It doesn't freeze. It doesn't require a round trip to the cloud to decide what to do next. It operates the way a competent staff officer would if they lost comms with higher headquarters — stay within the commander's intent, keep executing, document your decisions.
Second, human recoverability. When the operator reconnects — maybe from a phone on a Starlink connection, maybe from a basement after a power outage — they can audit everything the agent did, override decisions, and redirect. Full accountability, no gaps. The agent exercised judgment within bounds; the human reviews and adjusts.
These two constraints produce three operational modes. Automatic: agent executes within defined parameters, all actions logged. Semi-automatic: agent proposes, human approves — the default when connected. Manual: human directs each step, reserved for high-consequence operations. The mode shifts based on conditions, not preferences.
Moving Target Defense: offense validates defense
Static infrastructure is a gift to attackers. Stable IP addresses, persistent credentials, predictable network topology — it's a target set that doesn't move. Moving Target Defense changes the equation through agent-driven dynamic reconfiguration: rotating addresses, cycling credentials, relocating workloads, segmenting dynamically. The digital staff officer coordinates these shifts based on awareness of the current threat state, not on a fixed schedule.
Here's the counterintuitive part: MTD gets stronger under DDIL. The same infrastructure instability that degrades your connectivity also disrupts the attacker's persistence. If your defenses are already designed to reconstitute and adapt, degradation becomes a feature rather than a vulnerability.
Cracken validates these architectures by acting as the attacking agent — probing adaptive infrastructure the way a real adversary would, finding the gaps that static testing misses.
PETIO: building offensive capacity as a system
We utilize a framework called PETIO — People, Exploits, Technologies, Infrastructure, Operations — to map how agentic AI transforms each dimension of offensive cyber capacity. The PETIO framework, a conceptual model introduced by scholar Max Smeets, provides a systematic structure for analyzing the profound impact of agentic Artificial Intelligence (AI) on the various dimensions of offensive cyber capacity. Agentic AI refers to sophisticated AI systems capable of autonomous action, decision-making, and interaction within an environment, including the digital domain.
Smeets' framework is designed to map precisely how this transformative technology influences five key components essential for any state or non-state actor to execute successful offensive cyber operations. Each letter in the acronym PETIO corresponds to one of these critical dimensions:
- P - People:
- E - Exploits:
- T - Technologies:
- I - Infrastructure:
- O - Operations:
In essence, the PETIO framework serves as a vital analytical tool for policymakers, military strategists, and cybersecurity professionals to understand, predict, and mitigate the sweeping changes brought about by the integration of agentic AI into the domain of offensive cyber warfare. It highlights that the transformation is systemic, affecting every layer of a nation's cyber capacity.The key insight is that most of the tools already exist. The bottleneck isn't capability, it's coordination. And coordination is precisely where the digital staff officer earns its keep.
This technology significantly augments the human operator's capabilities, enabling a "commander" to be "effective with fewer resources" and promoting lean, impactful operations. The core principle is that "People remain the strategic center," with technology serving as the critical enabler for human judgment and leadership. This model decentralizes sophisticated command capabilities, exemplified by the image of the "operator with a phone," making high-level functionality mobile, distributed, and manageable by a single, well-trained individual.
Exploits and technologies gain force through orchestration and memory. An agent that can discover available tools, invoke them in sequence, chain their outputs, and remember what it learned across sessions is categorically different from a script that runs the same playbook every time. Memory is what makes a staff officer useful — they know what happened yesterday and adapt today's plan accordingly. Integration through open protocols like MCP means the staff officer works with existing SOC, C2, and cloud toolchains rather than requiring a rip-and-replace.
Infrastructure must rebuild itself. In DDIL, you can't assume anything stays up. Programmable infrastructure with threshold-based triggers, multi-region launch capabilities, and pre-authorized governance means the system reconstitutes without waiting for human intervention — and the human can review the decisions after the fact.
Operations follow a plan-execute-adapt cycle. The staff officer decomposes the plan, schedules execution, runs parallel sub-operations, and logs everything. Under DDIL, it continues within scope and resumes from last known state when conditions improve. Strategy stays with humans. Execution and coordination are delegated. Audit is mandatory, not optional.
From annual pentest to continuous validation
Periodic security assessments assume the environment holds still between tests. In an active conflict zone — or any environment facing sophisticated persistent threats — that assumption is wrong. The environment changes daily. The only valid posture is continuous validation.
Cracken runs persistent, agent-driven adversarial emulation. The platform plans penetration tests either autonomously, semi-autonomously, or with 100% human oversight, breaks them into parallel sub-operations across multiple attack vectors, and builds a live knowledge graph called Cybergraph that maps the relationships between assets, vulnerabilities, and credentials as it discovers them. This isn't a report you read once a quarter. It's an adversarial engine running continuously, finding what changed since yesterday.
Governance has to keep up
The best architecture in the world doesn't matter if procurement takes eighteen months to approve it. Governance frameworks need to accelerate the integration of battlefield-validated capabilities, not bottleneck them. Public-private partnerships have to be structured around operational speed. Procurement pathways have to accommodate technology that was proven in conflict, not just certified in a lab.
Countries that figure this out will have a structural advantage in cyber resilience. Those that don't will keep buying last year's solution through next year's procurement cycle.
What we're building toward
The future we see is agent-based systems under human strategic command — digital staff officers that translate intent into action across both defensive and offensive domains. Designed for DDIL from the ground up. Accountable through human-in-the-loop architecture at every level. And validated not in a simulation, but in the most demanding operational environment on earth.
Cracken is built by the people who operate in that environment. The framework we presented in Kyiv isn't theory. It's architecture drawn from what works when everything else breaks.
Jesse Nuese is Head of Business Development, Vlad Tereshyn is Software Engineer, and Dr. Oleksii Baranovyski is Chief Cybersecurity Researcher at Cracken. This post is adapted from their presentation at the Kyiv International Cyber Resilience Forum 2026.

